BLOGS
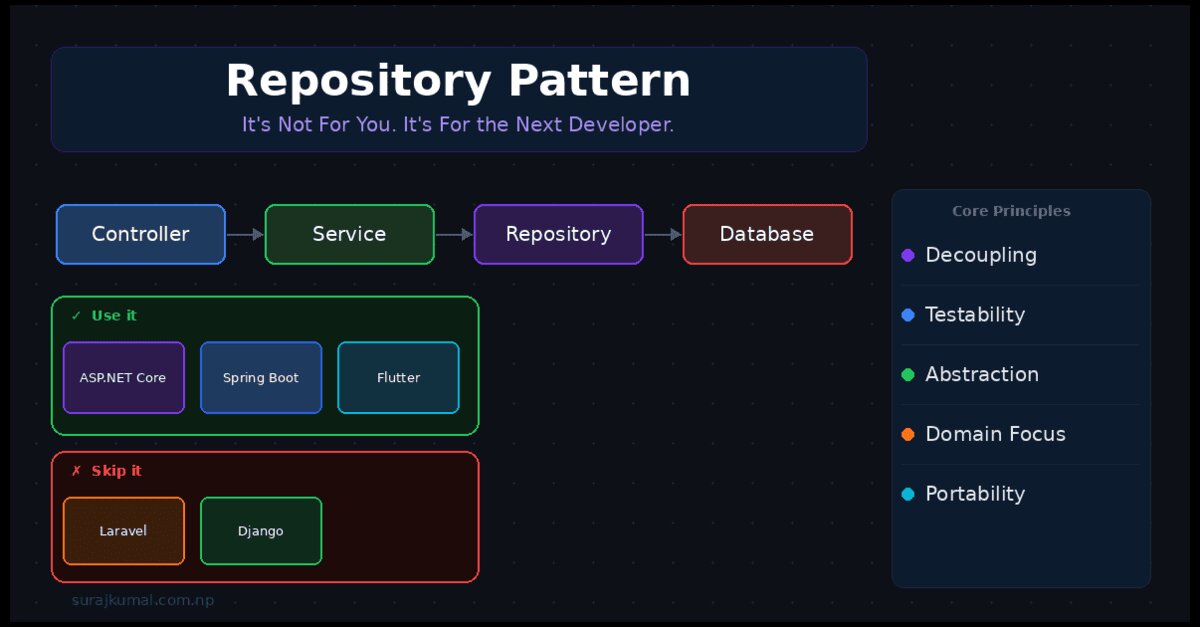
Repository Pattern: It's Not For You, It's For the Next Developer
The repository pattern isn’t universal - it’s contextual. It adds clarity in ASP.NET Core, Spring Boot, and large Flutter apps, but can be overkill in Laravel or Django where ORMs already abstract data. Its real value is communication . Helping developers maintaining codebases .
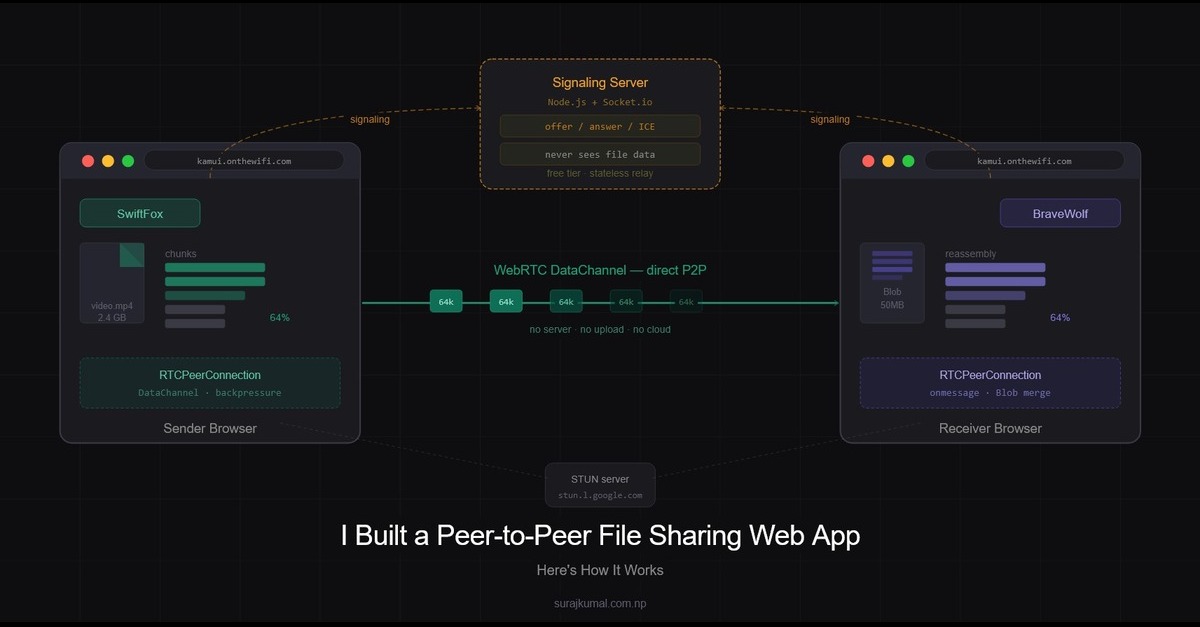
I Built Peer-to-Peer File Sharing Web App - Here's How It Works
A deep dive into Kamui, a browser-based peer-to-peer file sharing web app built with WebRTC and Socket.io. This post explains how direct device-to-device transfer works without uploads, servers, or installations including signaling, chunking, and real-world tradeoffs.

Web Shell Attacks: How a Single Uploaded File Becomes a Server Backdoor
File uploads seem routine—but weak validation can turn them into entry points. Web shell attacks let attackers upload scripts that execute via a browser, giving full server control. This covers how it works, real CVEs, and secure handling in PHP, Java, and .NET.
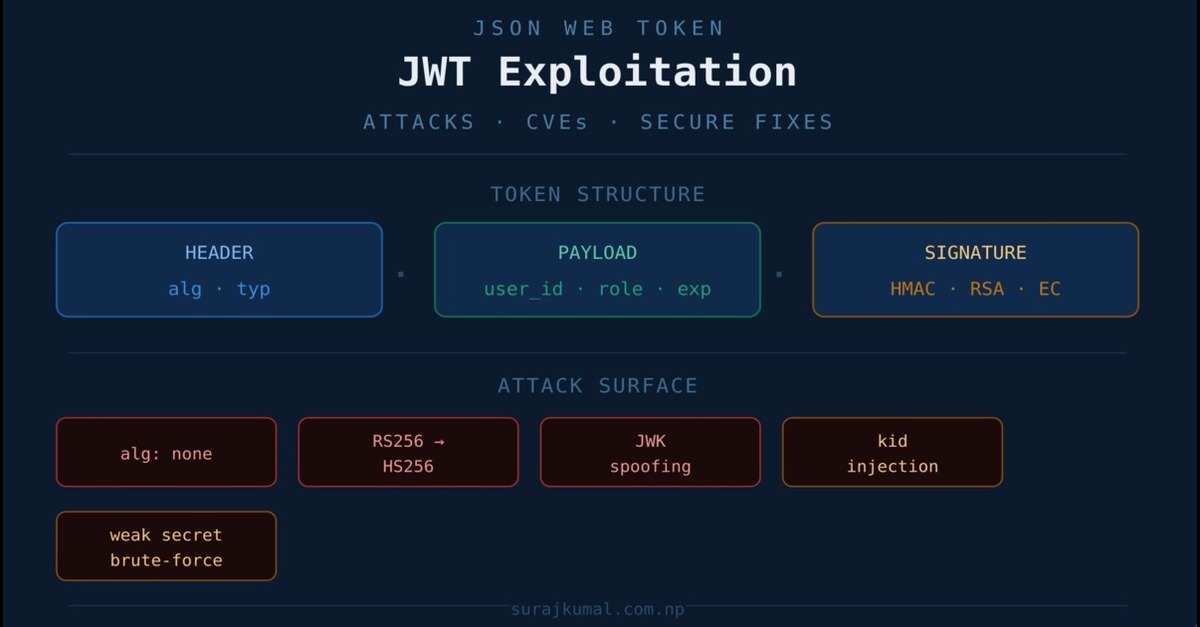
JWT exploitation: attacks, real CVEs, and secure fixes
JWTs are everywhere and so are the misconfigurations that break them. This post covers 5 real attack techniques including alg:none bypass, algorithm confusion, JWK spoofing, kid injection, and weak secret brute-force with real CVEs and secure fixes .